This newsletter is a free publication by the Institute for Secure Activism (ISA), a 501(c)(3) nonprofit organization dedicated to promoting personal security for activists, advocates, and the organizations that support them. ISA provides training, workshops, education materials, technical solutions, and technical consulting to civil rights and social justice advocacy organizations focused on LGBTQIA+, BIPOC, and other marginalized communities. Please consider making a tax-exempt donation to support our mission.
Can the FBI Read Signal Messages?
This morning The Guardian reported that the FBI spied on a Signal group chat of immigration activists. The article begins “The FBI spied on a private Signal group chat of immigrants’ rights activists who were organizing ‘courtwatch’ efforts in New York City this spring.”
Can the FBI read our Signal messages?!? The TL;DR is: No, unless someone GIVES our Signal messages to them. As confirmed in The Guardian article, the FBI was able to access those activists’ chat messages because they allegedly had access to someone in the chat. The records obtained by Property Of The People and provided to The Guardian state that the FBI obtained copies of the Signal chat from a “sensitive source with excellent access”. In other words, someone in that Signal chat was either an FBI agent or a “confidential informant” i.e. a snitch.

This situation is what folks in the information security “infosec” community call an “insider threat.” The best encryption technology is irrelevant when someone betrays our trust. When we consider our personal and organizational threat models it’s important to look at the places where sensitive information is vulnerable: who has access to unencrypted messages, documents, calendars, and other plans?
In another activist group chat this morning, an experienced organizer summed up the issue perfectly (reprinted with permission): “It’s a good reminder that this is one of the most likely scenarios in terms of security risk, and one that Signal’s end-to-end encryption doesn’t protect us from. People are vetted before joining this group, but the desire to have a low barrier to entry and to be welcoming to people who are new to organizing means that this will always be a risk we face. It’s hard, but helpful to get into the habit of assuming that what you say on here could end up in the hands of law enforcement or other bad actors.”
What about WhatsApp?
We’re still confident in Signal’s ability to protect our communications and metadata (data about data, more on that below). But what about other, more popular messaging apps? WhatsApp, by Facebook’s parent company Meta, is the most popular “commercial messaging app” (CMA) worldwide in 2025 and the second most popular in the United States (SimilarWeb).
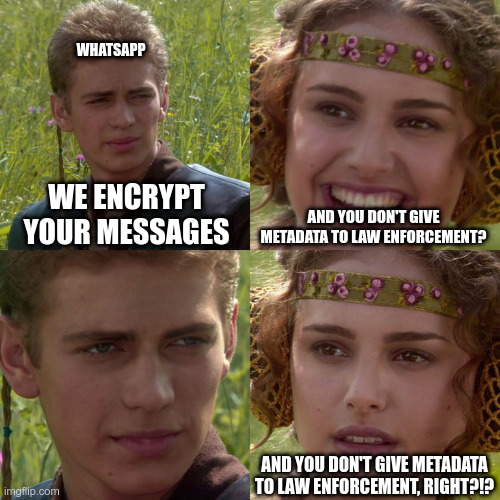
WhatsApp has actually used the same encryption as Signal since 2016. However, encrypting the content of a message isn’t enough to protect users’ privacy. Metadata must be protected as well. Metadata is “data that describes other data, as in describing the origin, structure, or characteristics of computer files, webpages, databases, or other digital resources.” (Wordnik) When you send a text message with any app, information about you, about the recipient, and about the message itself can be as important to law enforcement as the actual content of the message.
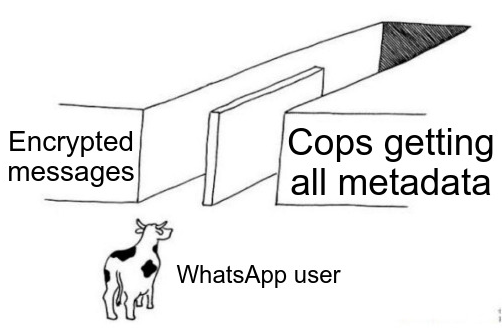
According to the Freedom of the Press Foundation, the metadata collected by WhatsApp includes the sender of the message, the receiver of the message, the date and time the message was sent, the time the message was sent, the digital size of the message, the approximate location of the device that the message was sent from, and the approximate location of the device that the message was delivered to. The Foundation’s article goes further, pointing out that “the WhatsApp privacy policy makes clear that Meta stores information about your profile, your contacts, when you are using the app and for how long, who you’re chatting with, details about the type of device you’re using (including if your operating system is up-to-date and how charged your battery is!), your location, and more.”
In contrast, Signal collects “technical information to the minimum required to operate the Services.” Signal, when subpoenaed, has repeatedly demonstrated that the only information they’re able to respond with is an account’s creation date and the last time that account was active. Signal does not collect or retain any other metadata. WhatsApp, on the other hand, collects so much metadata that ICE has a robust WhatsApp surveillance capability.
The Bottom Line
WhatsApp protects what you actually say to each other, but regularly provides information to law enforcement about who you speak to, when, and where. Signal protects absolutely everything except the fact that you’re using your Signal account. Signal is technically incapable of providing any additional information to law enforcement: they don’t have that information to give, even if they wanted to comply.
Thank you!
As always, thanks for subscribing and please send me your questions and comments! We’re all in this together.
We take care of us, we keep our community safe, we look out for each other. Go do good work!
